Executive Summary
- Architecture choice is the most decisive step in a strong RFP, and getting it right before issuance is one of the most effective ways to reduce risk and maximize long‑term impact.
- Physical, digital, and phygital models deliver fundamentally different results in deterrence, intelligence, enforcement, and public trust.
- Phygital architectures combine the strengths of physical and digital approaches, enabling deterrence, actionable intelligence, inter‑agency coordination, and citizen participation.
- Once embedded in the RFP, architecture choices effectively lock in enforcement capability, inter‑agency collaboration, citizen engagement, and audit defensibility - and are rarely reversible without significant political, operational, and financial cost.
The Architecture Choice: Physical, Digital, or Phygital?
Welcome to Chapter 2 of Implementing a Revenue Management & Control Solution.
In Chapter 1 (Part I and Part II), we focused on what must be resolved before the RFP: national risk, institutional alignment, and strategic intent. Chapter 2 moves to the next decisive phase: designing a strong RFP that can succeed in practice.
This article addresses the first and most consequential design choice governments must make: What type of architecture should the program be based on: physical, digital, or hybrid (phygital)?
This is a structural decision that determines what outcomes a program can realistically deliver over its lifetime. The purpose of this article is not to prescribe a single technical implementation, but to help governments frame their RFP around outcomes and ensure that proposed solutions are evaluated against the outcomes they must deliver, not just the technologies they use.
Architecture Choice is an Outcome Decision
One of the most common pitfalls in revenue protection tenders is specifying components instead of capabilities and outcomes. Governments list stamps, codes, databases, or scanners without first defining what the system must achieve in terms of deterrence, detection, intelligence, enforcement coordination, and public trust.
A strong RFP does the opposite. It starts by asking:
- What risks must be reduced?
- What decisions must this system support?
- Who must be able to act, and with what information?
Broadly, governments have three architectural models, each corresponding to a distinct risk profile. When an architecture is selected and embedded in the RFP, governments are determining which risks will remain structurally unaddressed for the lifetime of the program.
Architecture determines:
- how early illicit activity can be detected
- how reliably agencies can coordinate
- how defensible enforcement outcomes are under audit
- how much public trust the system can generate
Each architectural model therefore represents a distinct risk posture, not a technical preference.
Each model mitigates certain risks while leaving others exposed. In high‑exposure environments, architecture choice becomes less about preference and more about which residual risks a government is prepared to carry.

Physical solutions: high visibility, limited intelligence
Physical solutions rely primarily on tax stamps or security labels applied to products. These stamps carry overt, semi-covert, and covert security features designed to demonstrate that duty has been paid and to enable in‑field authentication by inspectors.
- Overt (visible): Designed for quick verification by consumers or customs agents without tools. Examples include holograms, color-shifting ink, and watermarks.
- Covert or semi-covert (hidden): Those are invisible to the naked eye and verified using specialised handheld devices and detection algorithms.
Structural strengths
Physical solutions are particularly effective at:
- creating visible deterrence at retail
- sending a clear consumer signal that products are regulated
- supporting enforcement in environments with limited connectivity
- providing immediate, low‑friction checks for frontline officers
For governments launching revenue protection for the first time, physical stamps can establish a baseline of control and visibility relatively quickly.
Structural limitations
However, physical-only architectures have inherent constraints:
- They generate no supply chain intelligence on their own
- They cannot detect diversion patterns or replication at scale
- They rely heavily on manual inspection and human judgment
- Sophisticated counterfeiters can replicate physical features
- Enforcement remains reactive, not predictive
Decision risk profile
Physical-only architectures reduce retail‑level ambiguity but leave governments structurally exposed to:
- late detection of organised diversion
- limited cross‑agency intelligence correlation
- high reliance on manual enforcement judgement
As a result, enforcement remains mainly reactive, and decision‑makers retain limited evidence to demonstrate control beyond visible deterrence.
Digital solutions: intelligence without visible authority
Digital models rely on unique serialized identifiers (e.g., DataMatrix or QR codes) assigned to each product unit and recorded at every point of the supply chain. Identity, movement, and event data are stored in a centralized system accessible to authorities.
Structural strengths
- Capturing end‑to‑end traceability data
- Detecting diversion, duplication, and suspicious flows
- Enabling risk‑based enforcement and analytics
- Supporting cross‑agency intelligence sharing
- Scaling across products and geographies
They transform enforcement into a data‑driven operation, supporting more proactive and targeted interventions.
Structural limitations
Digital‑only solutions also have trade‑offs:
- Limited visible deterrence at the POS
- Authentication becomes less intuitive for citizens
- Enforcement may remain “invisible”, if not operationalized well
- Field verification depends on devices and connectivity
- Public trust benefits can be harder to communicate
Decision risk profile
Digital-only architectures significantly strengthen intelligence generation but introduce other structural risks:
- Limited visible deterrence at retail
- Reduced intuitive verification for frontline officers and citizens
- Weaker public signalling of state control
In politically sensitive environments, this can make enforcement outcomes harder to explain and defend, even when data quality is strong.
Phygital solutions: converging risk reduction into a single model
Phygital solutions combine a physical security feature (stamp or label) and a machine‑readable digital identifier (2D barcode, DataMatrix, QR). The physical object becomes the carrier of its own digital identity, linking it directly to its supply chain record and enabling full traceability and real‑time monitoring.
Across jurisdictions with sustained enforcement outcomes, phygital architectures have emerged as the reference model, not because they are more complex, but because they are structurally better aligned with long‑term governance, enforcement coordination, and public accountability.
Phygital architectures capture the benefits of both worlds:
From physical systems:
- Visibility
- Deterrence
- Intuitive in‑field and consumer authentication
From digital systems:
- End‑to‑end traceability
- Predictive intelligence
- Cross‑agency coordination
- Scalable analytics
Advantages
Phygital architectures enable governments to:
- Authenticate products during in-field operations at the border, warehouse, retail
- Correlate field scans with supply chain data in real time
- Detect counterfeit replication before it floods markets
- Coordinate Customs, Tax, Health, and Enforcement from one source
- Extend verification to consumers without exposing sensitive data
Citizen verification as a force multiplier
A defining feature of phygital programs is citizen participation. When a citizen scans a regulated product and receives an instant authenticity response, enforcement capacity scales beyond agencies alone. Therefore, consumers become:
- early detectors of suspect products
- trust builders for compliant markets
- a visible extension of regulatory presence
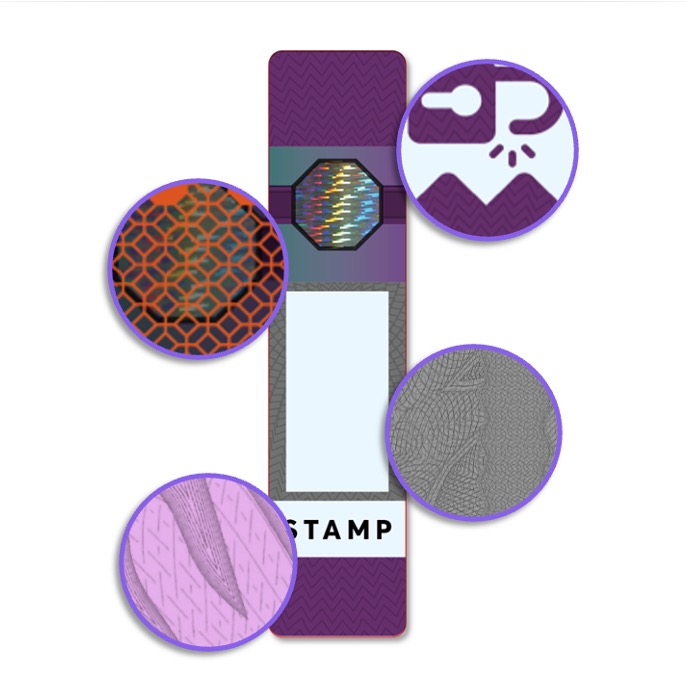

The next generation of tax stamps: visibility + intelligence
Decision risk profile
Phygital architectures are increasingly adopted by the most resilient national programs because they reduce multiple risk categories simultaneously:
- Operational risk, through real‑time intelligence
- Enforcement risk, through coordinated agency access
- Political risk, through visible and explainable control
- Audit risk, through end‑to‑end traceability linked to physical evidence
By converging deterrence, intelligence, and public verification into one system, phygital models offer the lowest combined institutional exposure over the program lifecycle. In practice, this enables authorities to demonstrate control simultaneously to auditors, legislators, enforcement bodies, and the public.
For these reasons, Inexto recommends a phygital architecture. It is the direction converging across international standards and the most resilient national programs, reflecting a shared recognition that long‑term enforcement credibility requires both visible control and data‑driven intelligence.
Architecture choice: Comparative Risk Summary
Architectural model | Primary strength | Residual risk carried |
| Physical-only | Retail visibility & deterrence | Limited intelligence, reactive enforcement, weak audit defensibility |
| Digital-only | Supply chain intelligence | Low public visibility, harder political justification |
| Phygital | Deterrence + intelligence + trust | Lowest combined operational, political, and audit risk |
RFP Implication: Asking the Right Questions
Once architecture is understood as a risk posture, the role of RFP becomes clear: not to compare components, but to assess which proposal minimize long-term institutional exposure while delivering measurable outcomes.
A well‑designed RFP asks:
- How does the proposed architecture deter illicit activity at retail and distribution level?
- How does it generate actionable intelligence to support enforcement decisions?
- How does it support cross‑agency coordination from a shared source of truth?
- How does it scale over time as risks, products, or regulations evolve?
- How does it engage citizens as part of the control ecosystem?
- How does it balance visibility, intelligence, and trust without increasing operational burden?
These questions allow governments to assess solutions based on their real‑world enforcement impact, not just technical descriptions.
The Strategic Choice Based on Outcomes
Choosing between physical, digital, or phygital solutions is a strategic decision that determines what a revenue protection program can realistically achieve. Architecture defines how risks are addressed, how agencies collaborate, how intelligence is generated, and how trust is built with citizens and legitimate industry.
Programs that underperform rarely do so because of technology constraints; they underperform because the architectural foundation locked in limitations from the start. By framing architecture choices in terms of outcomes, governments create the conditions for systems that evolve, scale, and deliver sustained public value.
Getting this decision right before the RFP is issued is one of the most effective ways to reduce risk and maximize long‑term impact.
What Comes Next
With the architectural direction established, the next step in designing a strong RFP is defining how the program will be funded and sustained over time.
In Chapter 2 – Part II, we will examine the 3 main funding models governments use today:
- Government‑funded models
- Industry‑funded models
- Hybrid models
We will explore how each model affects governance, incentives, market acceptance, and long‑term sustainability – and how funding choices must align with the selected architecture to avoid unintended consequences.
The objective is not to promote a single model, but to help governments select a funding structure that reinforces program outcomes, preserves public interest, and ensures continuity across political and budget cycles.
Before the RFP
Designing a Strong RFP
Coming Soon
Coming Soon
Contact us
If your institution is evaluating physical, digital, or phygital revenue protection models, Inexto provides government‑only architecture briefings to assess the strengths, limitations, and outcome implications of each approach.
These sessions support ministries and regulators in selecting an architectural model aligned with national risk, enforcement capacity, and long‑term program objectives.
Contact us to request an institutional briefing.

